(Updated on 11/04/2020)
With season 3 of Mr. Robot coming back strong in its premiere, we took a closer look at some of Elliot’s hacking techniques. Hollywood films and TV shows are notorious for butchering how hackers really operate. Shows like CSI love to casually drop lines like "I'll create a GUI interface using visual basic to track the killer's IP address". With so many shows and movies getting it wrong, Mr. Robot changed the game with its authenticity. Let’s take a look at some of Mr. Robot's hacks as seen on screen and how you can prevent them.

Denial of Service
Scenario:
In episode 1 of season 1 All-Safe, a cybersecurity vendor outsourced by E Corp, notices a massive distributed denial-of-service (DDoS) attack targeting E CORP’s servers. A DDoS attack floods a resource with incoming traffic disrupting normal operations. This impacts the availability E Corp’s services and, the show tells us, in just one hour E Corp loses around 13 million dollars in revenue.
Preventive Measures:
The challenge with DDoS attacks is that the attack cannot be stopped by blocking a single source. Common methods to combat this type of attack would include:
-Implementing detection methods
-Overprovisioning of bandwidth
-Engaging your Internet Service Provider
-Using a DDoS vendor’s services
The Femtocell Hack
Scenario:
Elliot installs malicious code onto a Femtocell, a device that mimics cell phone towers, then has Angela place the device inside of the E Corp Build where the FBI is conducting an investigation. The plan is to intercept and download cell data from any FBI agent within a 100-foot radius.
Preventive Measures:
This is a tricky one because an insider was involved (we will get into that next) making this scenario even harder to detect and prevent. Angela’s actions aside, here are some common ways to detect and prevent varying types of rogue access points:
-Implement IDS/IPS systems
-Continuous scanning for rogue devices
-Remediation processes for rogue devices

Insider Threats
Scenarios:
Angela’s actions at E Corp show just how dangerous a malicious insider can be to an organization. With her authorized physical and digital access, she is able to set up a rogue access point and abuses her access to steal data. In another scene, Elliot uses the access he has been granted by All-Safe to access a large customer’s network. With remote access, Elliot installs a backdoor that he eventually uses to launch a major attack. The attack ends up encrypting all of E Corp's digital data and backups.
Preventive Measures:
As defined by US Cert, an insider threat is when a user—a trusted vendor, privileged user or business user—intentionally or unintentionally misuses access to negatively affect the confidentiality, integrity, or availability of the organization’s critical information or systems. Insider threat can be difficult to prevent because the user has already been granted authorized access. Here are some common best practices in mitigating the risk of insiders:
-Monitor user activity
-Detect unauthorized activity
-Control access to information
-Monitor data access and movement
-Enforce company policies
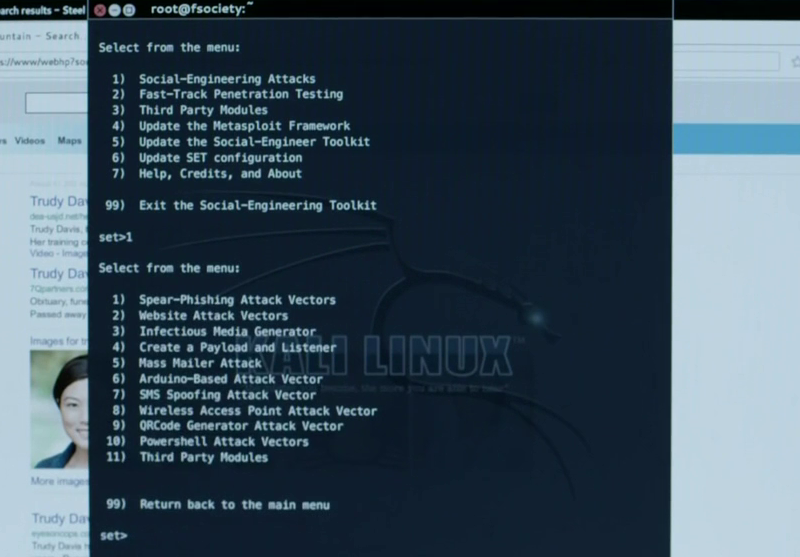
Social Engineering
Scenarios:
Elliot enters Iron Mountain on a mission to gain access to the HVAC network. To achieve this goal, Elliot and team create a fake identity of a high-profile guest to get a private tour of the facility. While on a tour, Elliot yells at the tour guide to get a supervisor. When the supervisor arrives, Elliot's team sends a fake text message causing the tour guides to run off. This leaves Elliot free to roam around the facility. In another scene, while being tailed by the FBI, a member of the dark army calls into N-Star to report a stolen car. N-Star has the ability to govern a car if there is a belief it has been stolen; by socially engineering the N-Star representative, the dark army is able to lose the trailing car.
Preventive Measures:
Hackers frequently prey on unassuming people by exploiting common human interactions. The best way to mitigate the risk of social engineering is to educate employees. Training should include how to recognize a phishing email, create and maintain strong passwords, avoid dangerous applications, ensure valuable information is not taken out of the company in addition to other relevant user security risks.

Removable media
Scenarios:
In season 1, Elliot and Darlene try to gain access into a prison by dropping USBs containing malware in the parking lot of the facility. One of the prison guards picks up the removable device and plugs it into a workstation. Luckily for the station, the malware was detected and contained by an Endpoint Protection Platform (EPP) tool. In another scene, Angela puts a CD containing malicious software into an all-safe corporate system. This enables the dark army to gain access to both all-safes and all of their customer's networks.
Preventive Measures:
Removable media can cause a number of headaches from data loss to intrusion. Here are a few controls that can be put in place:
-Lockdown USB ports
-Monitoring user activity
-Endpoint protection (EPP) tools
-Employee education
-Enforce company policies
Subscribe to the Proofpoint Blog

